Exploit Development
Oct 27, 2010
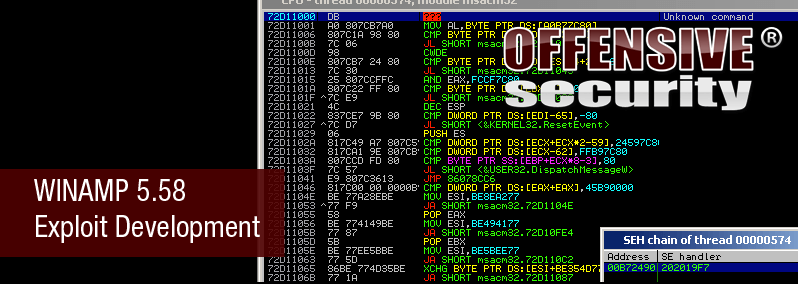
Winamp 5.58 Exploit Development
The guys at the Exploit Database posted an awesome writeup on a Winamp 5.58 Exploit Development storming session – with some really cool results. In the end, they ended up writing a short assembly sequence to walk through the payload and replace bad characters with original shellcode bytes.
 The guys at the Exploit Database posted an awesome writeup on a Winamp 5.58 Exploit Development storming session – with some really cool results. In the end, they ended up writing a short assembly sequence to walk through the payload and replace bad characters with original shellcode bytes. Read more – Winamp 5.58 from Dos to Code Execution
The guys at the Exploit Database posted an awesome writeup on a Winamp 5.58 Exploit Development storming session – with some really cool results. In the end, they ended up writing a short assembly sequence to walk through the payload and replace bad characters with original shellcode bytes. Read more – Winamp 5.58 from Dos to Code Execution