Kali Linux
Apr 5, 2010
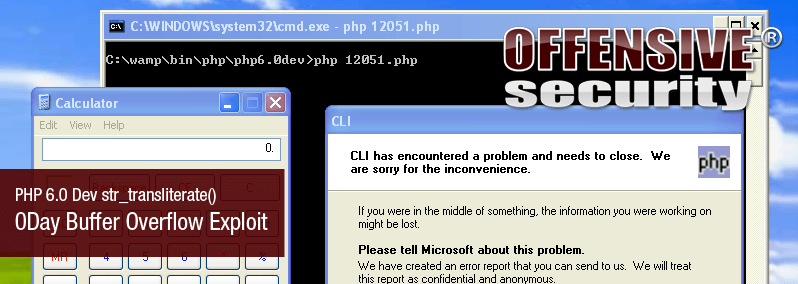
PHP 6.0 Dev str_transliterate() 0Day Buffer Overflow Exploit
An interesting submission to EDB today from the guys at http://www.nullbyte.org.il – a PHP 6.0 0day buffer overflow.
An interesting submission to the Exploit Database today from the guys at http://www.nullbyte.org.il – a PHP 6.0 0day buffer overflow.
From the exploit comments:
## This code should exploits a buffer overflow in the str_transliterate() function to call WinExec and execute CALC
## Take a look, 'unicode.semantics' has to be on!
## php.ini > unicode.semantics = on
Their exploit code was tested and verified by the EDB team – check it here.
Stay in the know: Become an OffSec Insider
Get the latest updates about resources, events & promotions from OffSec!

