Blog
Dec 4, 2013
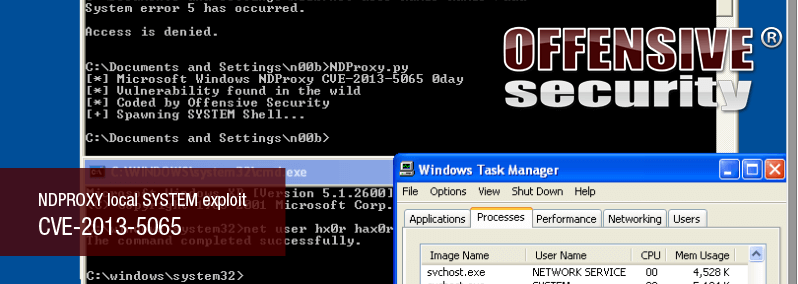
NDPROXY Local SYSTEM exploit CVE-2013-5065
In the past few days there has been some online chatter about a new Windows XP/2k3 privilege escalation, well documented by FireEye. Googling around, we came across a Twitter message which contained a link to a Chinese vulnerability analysis and PoC.
1 min read
Author: Matteo Memelli
In the past few days there has been some online chatter about CVE-2013-5065, a new Windows XP/2k3 privilege escalation, well documented by FireEye. Googling around, we came across a Twitter message which contained a link to a Chinese vulnerability analysis and PoC for CVE-2013-5065.
Due to the fact that the extended instruction pointer is set to 0x00000038 at the time of the crash, this bug can easily be exploited on Windows XP, which offers little resistance, as it allows non-privileged users to map the null page within the context of a user process. From there, it was trivial to produce a fully working exploit, which we will have posted on the Exploit-DB.
To read more about the Microsoft recommendations for dealing with this vulnerability so that you are not unduly exposed.
Stay in the know: Become an OffSec Insider
Get the latest updates about resources, events & promotions from OffSec!
Latest from OffSec

Research & Tutorials
CVE-2024-13059: Exploiting Path Traversal in AnythingLLM for Remote Code Execution
Discover CVE-2024-13059, a critical vulnerability flat that affects AnythingLLM’s handling of ASCII filenames in the multer library.
Apr 17, 2025
2 min read

Enterprise Security
How OSCP Holders Can Lead Their Teams to Greater Cybersecurity Resilience
Champion OSCP training in your organization to build a unified, resilient security team.
Apr 11, 2025
6 min read

Research & Tutorials
CVE-2024-57727: Path Traversal Vulnerability in SimpleHelp Web Application
CVE-2024-57727 lets attackers read sensitive files via path traversal in SimpleHelp. Learn more about how attackers exploit this flaw.
Apr 10, 2025
3 min read
