Blog
Jan 15, 2010
Multiple Media Player HTTP DataHandler Overflow
Multiple Media Player HTTP DataHandler Overflow submitted to Exploit-db.
2 min read
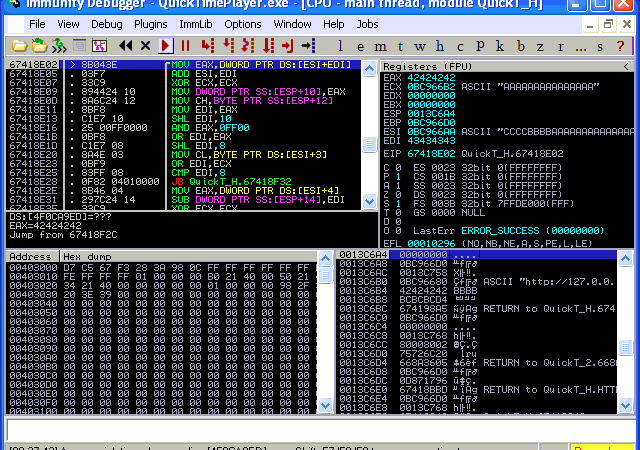
We recieved an interesting submission today at exploit-db from Dr_IDE. We have verified that both Quicktime and Itunes crash on Windows and OSX. The description reads:
 “There is a widespread failure in the way that (.MOV) files are handled by the Quicktime Library. I have attempted to compound my findings on this issue.
“There is a widespread failure in the way that (.MOV) files are handled by the Quicktime Library. I have attempted to compound my findings on this issue.
Nearly every (.MOV) enabled application that I tested fell victim to this exploit. This is a local memory corruption vulnerability in the way these programs process a malformed file. I have provided crash logs, register dumps where applicable, sample script and trigger file.
Memory Corruption is repeatable and code execution seems possible. Because this issue affects web browsers it seems that the attack vector will be both Local and Remote.
It should be noted these applications are all registered by default as registered applications for this file type. There is no trickery involved in order to enable these programs to open the malicious file.”
Check it here
Cybersecurity leader resources
Sign up for the Secure Leader and get the latest info on industry trends, resources and best practices for security leaders every other week
Latest from OffSec

Research & Tutorials
CVE-2024-9956: Critical WebAuthentication Vulnerability in Google Chrome on Android
Discover CVE-2024-9956, a critical Chrome flaw on Android allowing Bluetooth-based PassKey theft, and learn key mitigation strategies.
Mar 26, 2025
3 min read

OffSec News
Learn Secure Java Development with OffSec’s New Course
Master secure Java coding with OffSec’s SJD-100 course. Enhance app security and gain hands-on experience to secure your coding practices.
Mar 18, 2025
4 min read

Insights
Creating an Inclusive Cybersecurity Culture
Transform your cybersecurity culture by strategically improving women’s representation and cultivating meaningful inclusion.
Mar 17, 2025
4 min read