May 3, 2010
Malicious Google Gadgets in Action
Malicious Google Gadgets in Action Video – by Offensive Security
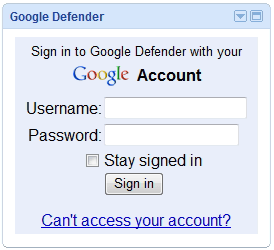
 A new report by emgent shows malicious Google Gadgets in action. The real vulnerability lies in the ability of a malicious user to add their own Gadgets on a separate domain space, without Google’s authorization.
A new report by emgent shows malicious Google Gadgets in action. The real vulnerability lies in the ability of a malicious user to add their own Gadgets on a separate domain space, without Google’s authorization.
The attack variant shown in the movie can be altered to steal cookies, run arbitrary JavaScript on victim machines, and could be further weaponized to create Malicious Google Gadget worms.
When researching this topic, we found references to similar vulnerabilities which date back to 2007, reported by Tom Stracener and Robert Hansen.
Although the Google infrastructure has changed since 2007, it seems that this new variant of attack is still possible. Emgent’s email to Google over a month ago was unanswered. The solution ? Extra vigilance on your side. Check our demo movie.