Nov 29, 2010
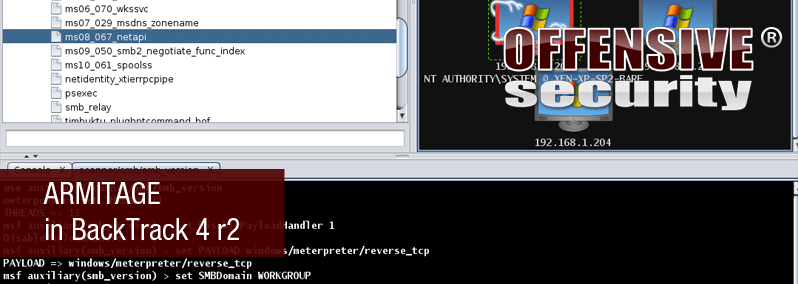
Armitage in BackTrack 4 r2
A brief time ago, an exciting GUI front-end for Metasploit named Armitage was released. For being an initial release, Armitage is very polished and so we knew we had to add it to the BackTrack respositories.
A brief time ago, an exciting GUI front-end for Metasploit named Armitage was released. For being an initial release, Armitage is very polished and so we knew we had to add it to the BackTrack respositories.
To install it, we first need to update the repositories.
[cc lang=”bash”]root@bt:~# apt-get update
…snip…
Reading package lists… Done[/cc]
Next, we simply need to install the armitage package.
[cc lang=”bash”]root@bt:~# apt-get install armitage
…snip…
Setting up armitage (0.1-bt0) …
root@bt:~#[/cc]
Prior to launching Armitage, we need to start the MYSQL server in BackTrack.
[cc lang=”bash”]root@bt:~# /etc/init.d/mysql start
Starting MySQL database server: mysqld.
Checking for corrupt, not cleanly closed and upgrade needing tables..
root@bt:~#[/cc]
Once the MYSQL server is started, we then need to start the Metasploit RPC daemon. You can assign whatever credentials you would like, of course.
[cc lang=”bash”]root@bt:~# msfrpcd -f -U msf -P test -t Basic
[*] XMLRPC starting on 0.0.0.0:55553 (SSL):Basic…[/cc]
Armitage is installed under /pentest/exploits/armitage/ so we navigate to the folder and run the shell script to begin.
[cc lang=”bash”]root@bt:~# cd /pentest/exploits/armitage/
root@bt:/pentest/exploits/armitage# ./armitage.sh[/cc]
When Armitage first launches, we are prompted to connect to the msfrpcd instance and our MYSQL database as shown below. We verify our settings, select Use SSL, and click Connect.
Running a quick smb_version scan against our local subnet reveals a number of Windows machines. The icon assigned to these targets indicates that they are either WinXP or Server 2003 machines.
We use the highly reliable exploit for MS08-067 to exploit one of our targets and the target graphic is changed to indicate that we have successfully compromised it.
With this initial target compromised, we can then dump the hashes from the system and leverage it with a psexec attack against the remaining hosts in our subnet to deliver 4 additional shells to us.
With very minimal setup and a few clicks, we have managed to get 5 Meterpreter shells on our target systems. Static images simply cannot do justice to this tool so you are encouraged to update BackTrack and test it out for yourself. The author of Armitage also has some excellent video demonstrations of the tool in action:



